Posts by Naomi
Weak Security WiFi: Risks and How To Strengthen Yours
An unsecured WiFi connection isn’t just a small hassle — it can open the door to hackers, data thieves, and other cybercriminals. Whether you’re at home, in a café, or at the office, weak WiFi security puts your data at risk. It can expose personal details, financial information, and everything you do online. What makes…
Read MoreSSPM vs CSPM: Key Differences Explained for Security
In today’s complex world, understanding the difference between SSPM and CSPM is essential. Each plays a critical role in defending your organization’s digital assets, but they do so in very different ways. Why does one focus on apps like Microsoft 365 while the other keeps an eye on giants like AWS and Google Cloud? How…
Read MoreWhat Is Network Automation? Essential Guide & Benefits
In today’s fast-moving IT landscape, network automation is transforming how we manage and maintain digital infrastructure. But what exactly does it do, and why are top tech teams making it a priority? Network automation unlocks powerful advantages, from eliminating repetitive tasks to boosting network reliability. But how does it actually work? And what role do…
Read MoreTCP vs HTTP: Key Differences Between TCP and HTTP Explained
When you load a website or stream a video, two powerful protocols are working behind the scenes: TCP and HTTP. But what exactly sets them apart? Why does one focus on reliability and the other on simplicity? And how do they work together to make your internet experience seamless? In this article, we’ll explore the…
Read MoreAlternative to FTP: Discover Better File Transfer Solutions
FTP, a protocol developed in the 1970s, is painfully outdated. It transmits data in plain text, making it vulnerable to breaches, and its transfer speeds can’t keep up with modern demands. But don’t worry, there are smarter options available. This article explains how SFTP and FTPS address FTP’s flaws. It also discusses why cloud-based platforms…
Read MoreNetwork Security: Key Strategies To Protect Your Systems
Do you think your business is safe from cyberattacks? Think again. With 90% of organizations hit by a cyberattack last year, the question isn’t if they will target you — it’s when. And when that moment comes, will your systems be ready? From multi-million dollar data breaches to phishing scams that slip through the cracks,…
Read MoreTypes of DDoS Attacks: Understand the Various Attack Forms
In today’s digital world, cyber threats are getting more complex. Distributed denial of service (DDoS) attacks are a big worry for companies. They can make online services unavailable, stopping users from accessing important resources. DDoS attacks have different types, each with its own features and challenges. Some attacks flood networks with traffic, while others are…
Read MoreWhat Is PGP Encryption? Learn About Secure Data Communication
Your inbox isn’t as private as you think. Every day, personal messages, business deals, and sensitive data fly across the internet — and plenty of it is up for grabs. Hackers, trackers, and even corporations are watching more than you realize. So how do you keep your conversations truly secure? There’s a powerful tool that…
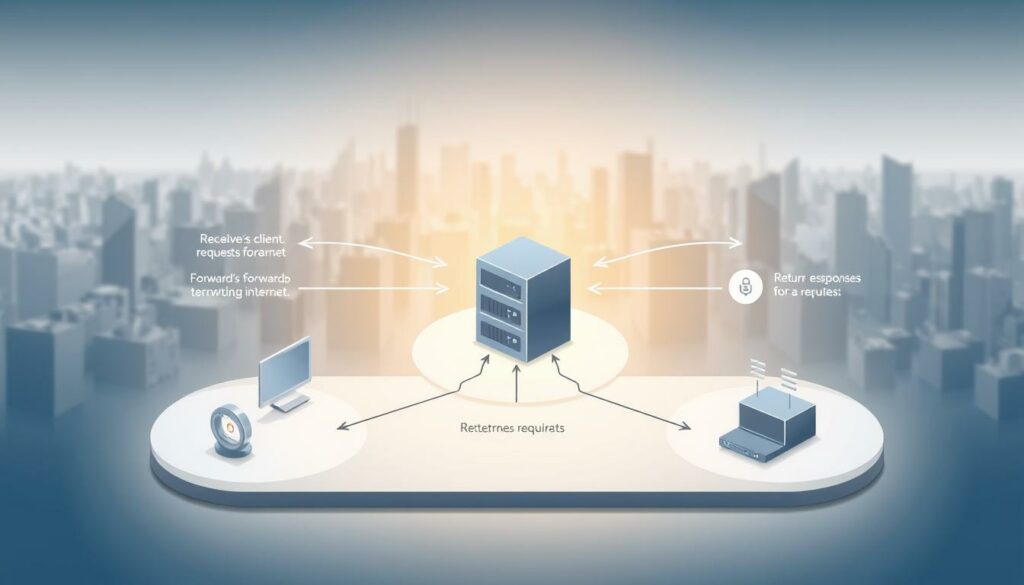
Read MoreWhat Is a Proxy Server? Benefits and How It Works Explained
Ever wondered what a proxy server is? Think of it as a digital middleman — an intermediary that stands between you and the websites you visit. It routes your internet traffic, masks your IP address, and can improve your security, privacy, and browsing speed. Cybercrime surged in 2021, with Americans reporting nearly 850,000 complaints across…
Read MoreTips To Consolidate Email Accounts for Greater Efficiency
Are you tired of managing many email accounts? It’s time to simplify your digital life by merging them. This can make you more productive and save you time. Did you know most people handle at least two email accounts? Some even manage three or four. This can really slow you down. But, there’s a way…
Read MoreBest P2P File Sharing Websites for Fast File Transfers
Speed and security matter when sharing large files, and traditional methods often fall short. That’s where P2P file-sharing websites come in. They allow direct transfers between computers without the need for slow, restrictive cloud storage or vulnerable email attachments. The demand for reliable file-sharing tools is skyrocketing. In 2022, 80% of U.S. workers wanted seamless…
Read MoreWhat Is Information Security Compliance?
In a world where data is currency, information security compliance isn’t just about ticking boxes—it’s about survival. It means following the laws, regulations, and industry standards that keep sensitive information safe from hackers, leaks, and costly breaches. But compliance isn’t a one-and-done deal. It requires proactive security measures, routine audits, and a workforce that understands…
Read MoreCloud vs Server: Key Differences You Should Know
Choosing between cloud and on-premises servers is a crucial decision for businesses. Cloud computing offers scalability, cost savings, and remote access, transforming IT management. On-premises servers provide full control over hardware and software, making them ideal for security-sensitive and highly customized applications. While cloud services reduce upfront costs and maintenance, traditional servers offer stability and…
Read MoreWhat Is a Live Document? Understanding Its Features
In today’s fast-paced digital world, businesses are moving beyond static files to embrace a more fluid, interactive way of working. Live documents are revolutionizing collaboration, making real-time edits and updates possible for teams everywhere. Imagine a digital workspace where ideas evolve instantly, where teams can refine reports, update plans, and fine-tune agreements. All without the…
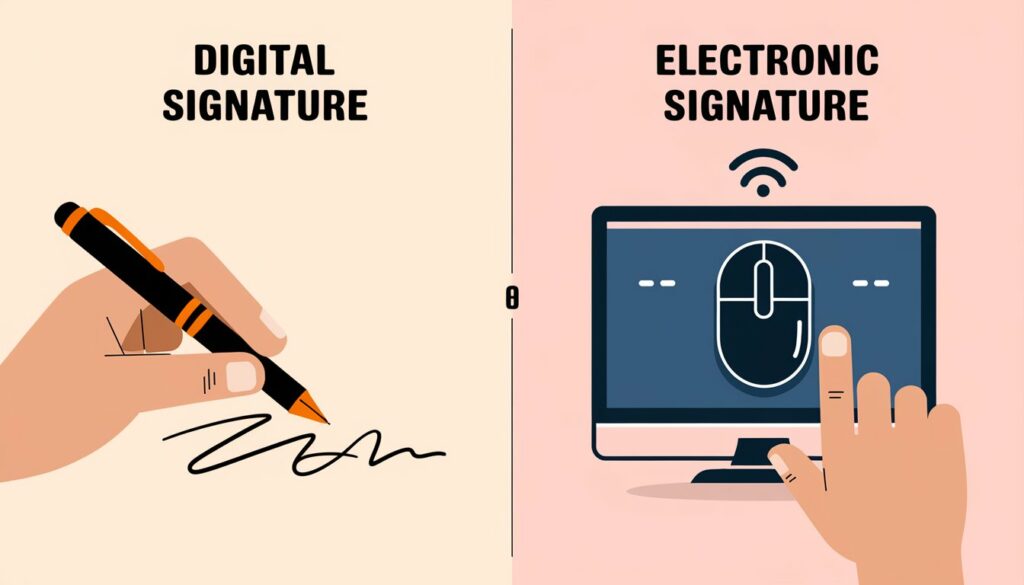
Read MoreDigital Signature vs Electronic Signature: What’s the Difference?
In today’s fast-paced digital world, signing documents has never been easier — or more complex. Whether you’re closing business deals, approving contracts, or verifying agreements online, you’ve likely come across the terms “digital signature” and “electronic signature.” They may sound similar, and many people use them interchangeably. But, in reality, they serve different purposes and…
Read MoreHow To Send Large Audio Files: Tips and Best Practices
Have you ever recorded the perfect podcast episode, a brilliant new track, or a crisp voiceover? Then, you hit a wall when you try to send it. The email says, “File too large.” Does it sound familiar? Well, you’re not alone. Many content creators, musicians, and podcasters run into this frustrating roadblock when trying to…
Read MoreWhat Is Electronic File Management? Complete Overview
Imagine never having to dig through piles of paperwork again. No more misplaced documents, cluttered desks, or wasted time searching for files. Electronic file management is transforming the way businesses handle information — making workflows faster, smarter, and more secure. By shifting from paper-based systems to digital storage, companies can streamline operations, enhance collaboration, and…
Read MoreHow To Send Documents Securely via Email: Easy Methods
Email is one of the most convenient ways to share documents, but it’s also one of the most vulnerable. Cyber threats, phishing scams, and data breaches can put your sensitive information at risk if you’re not careful. When sending business contracts, financial records, or personal documents, it’s crucial to implement the right security measures. But…
Read MoreWhy Is Digital Filing Important? Benefits for Your Business
Have you ever wasted precious time digging through piles of paper, only to find the document you need buried — or worse, missing? It’s a frustration most of us have faced, and it’s exactly why digital filing has become so important in today’s world. By moving from physical paperwork to a streamlined digital system, you…
Read MoreHow To Encrypt a File in Linux: Secure Your Data
Keeping your data safe is key in today’s digital age. Linux has strong tools for encrypting files, making it a top choice for protecting your information. This guide will show you how to use different encryption methods in Linux. Linux can encrypt text files, documents, and images. We’ll look at both command line and graphical…
Read MoreCloud Computing vs Traditional Computing: What You Need to Know
Technology isn’t just a tool — it’s the backbone of business growth and innovation. When it comes to managing your data and IT infrastructure, are you better off with the flexibility of cloud computing? Or with the tried-and-true stability of traditional computing? Each approach has its champions and critics, and the choice isn’t as clear-cut…
Read MoreKey Reasons Why Is File Management Important for Efficiency
In today’s fast-paced digital world, file management isn’t just a nice-to-have — it’s a cornerstone of productivity and efficiency. How you handle your files can make or break your workflow, whether you’re running a business, managing a team, or organizing personal projects. Think about this: a staggering 83% of workers waste valuable time redoing work…
Read MoreData Protection vs Information Security: Understanding the Gap
In today’s interconnected digital landscape, safeguarding data has become a top priority for businesses and individuals alike. With data breaches costing companies millions and eroding public trust, understanding the distinction between data protection and information security is more important than ever. Both concepts are critical for compliance, trust-building, and resilience. Data protection laws, such as…
Read MoreExploring the Cloud Data Lifecycle: Stages and Best Practices
In today’s fast-paced digital world, data isn’t just a resource — it’s your organization’s most valuable asset, shaping decisions, driving innovation, and fueling growth. Without a clear strategy to manage its journey from creation to deletion, even the most promising data can become a liability. The cloud data lifecycle isn’t just a buzzword — it’s…
Read MoreHow To Check if Gmail Is Blocking Incoming Emails
Have you ever waited for an important email that never seems to show up? It’s frustrating, right? The culprit might be Gmail itself. With its powerful spam filters and security features, Gmail does a great job of keeping unwanted messages out of your inbox. However, sometimes, it can block legitimate emails, too. If you’re wondering…
Read More